Cloudflare Client
- Classification
-
cloudflare
- Version
-
2.7
- Language
-
en
- Description
-
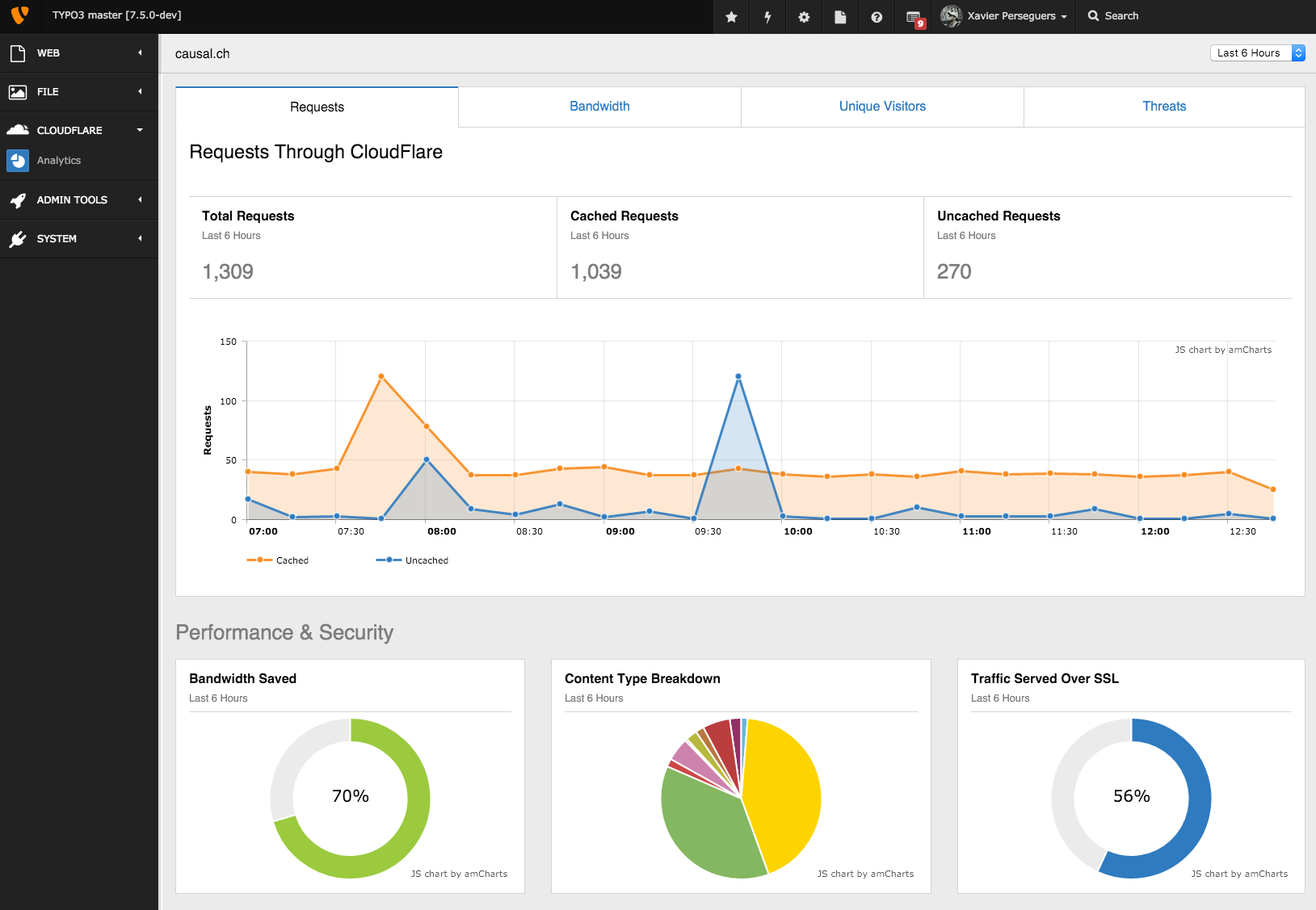
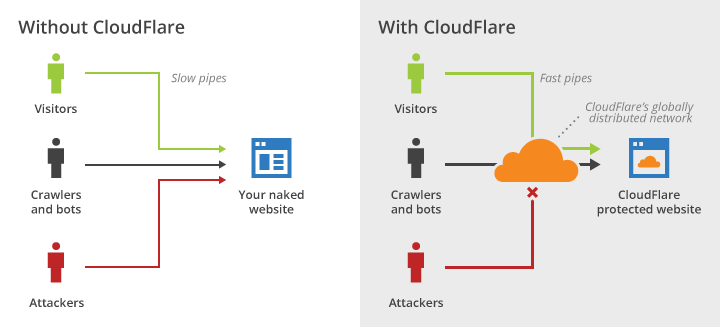
The Cloudflare extension for TYPO3 is a powerful solution to integrate your website with Cloudflare, whose mission is to help build a better Internet. This extension provides a variety of features to ensure your website is running optimally on the Cloudflare platform, a global leader in web performance and security.
- Keywords
-
cloud, content delivery network, cdn, proxy, reverse proxy, ssl, performance
- Copyright
-
2012-2026
- Author
-
Xavier Perseguers
- License
-
This document is published under the Open Publication License available from http://www.opencontent.org/openpub/
- Rendered
-
Tue, 24 Mar 2026 12:37:58 +0000
The content of this document is related to TYPO3, a GNU/GPL CMS/Framework available from www.typo3.org.
Table of Contents