FAL Protect
- Extension key
-
fal_protect
- Package name
-
causal/fal-protect
- Version
-
main
- Language
-
en
- Description
-
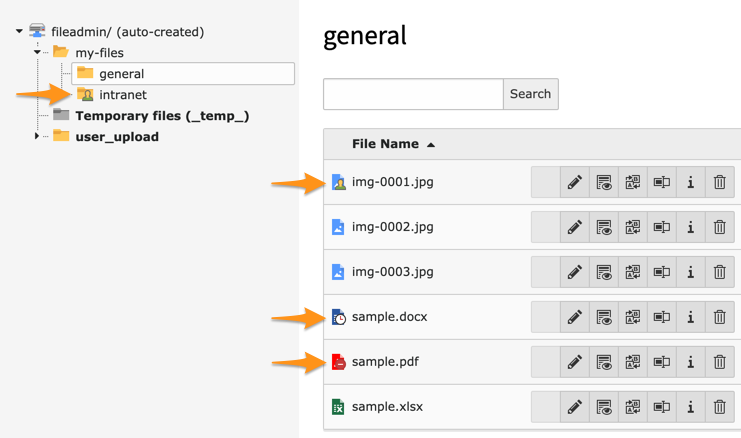
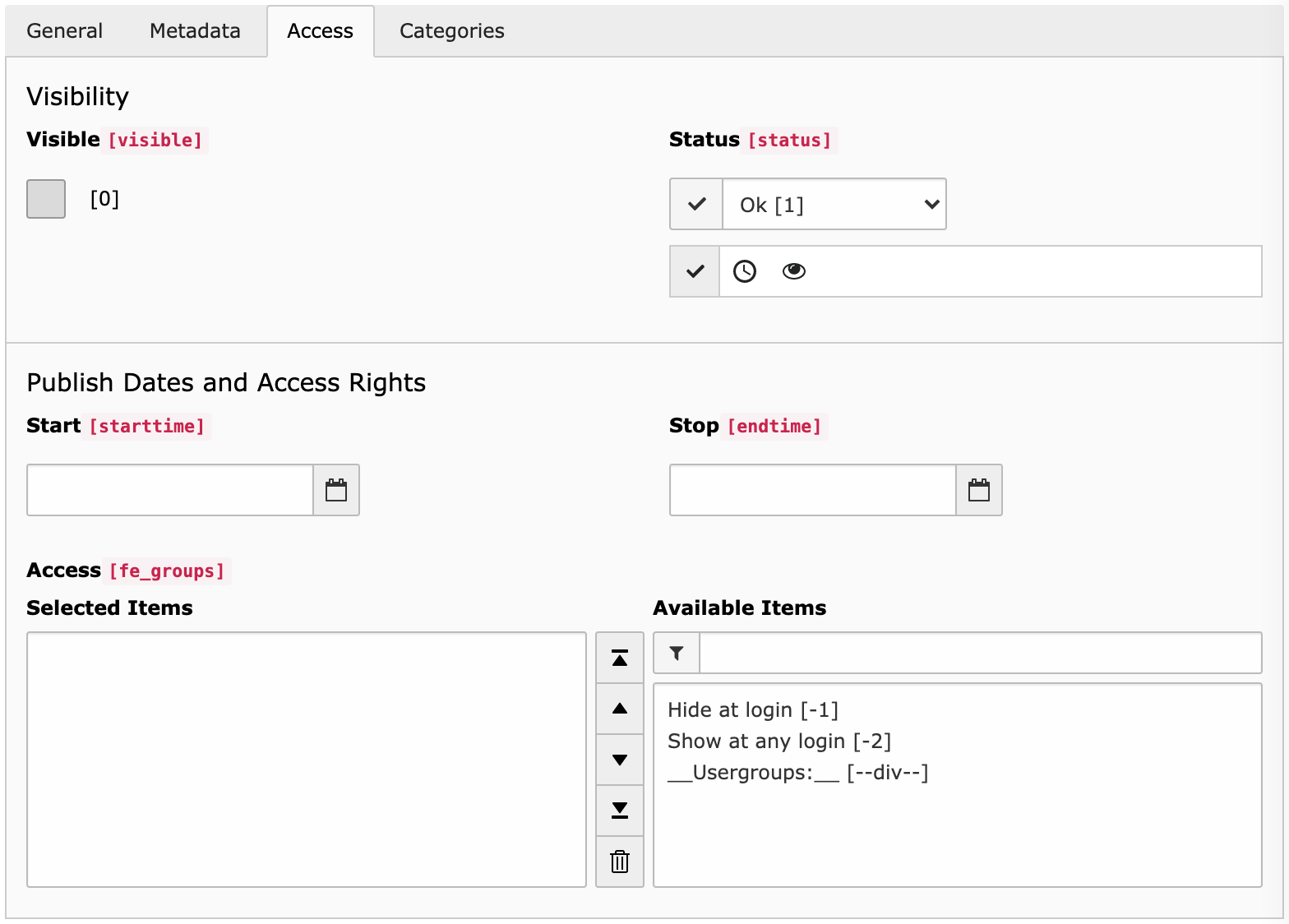
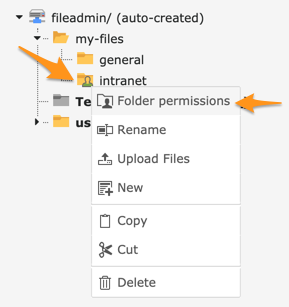
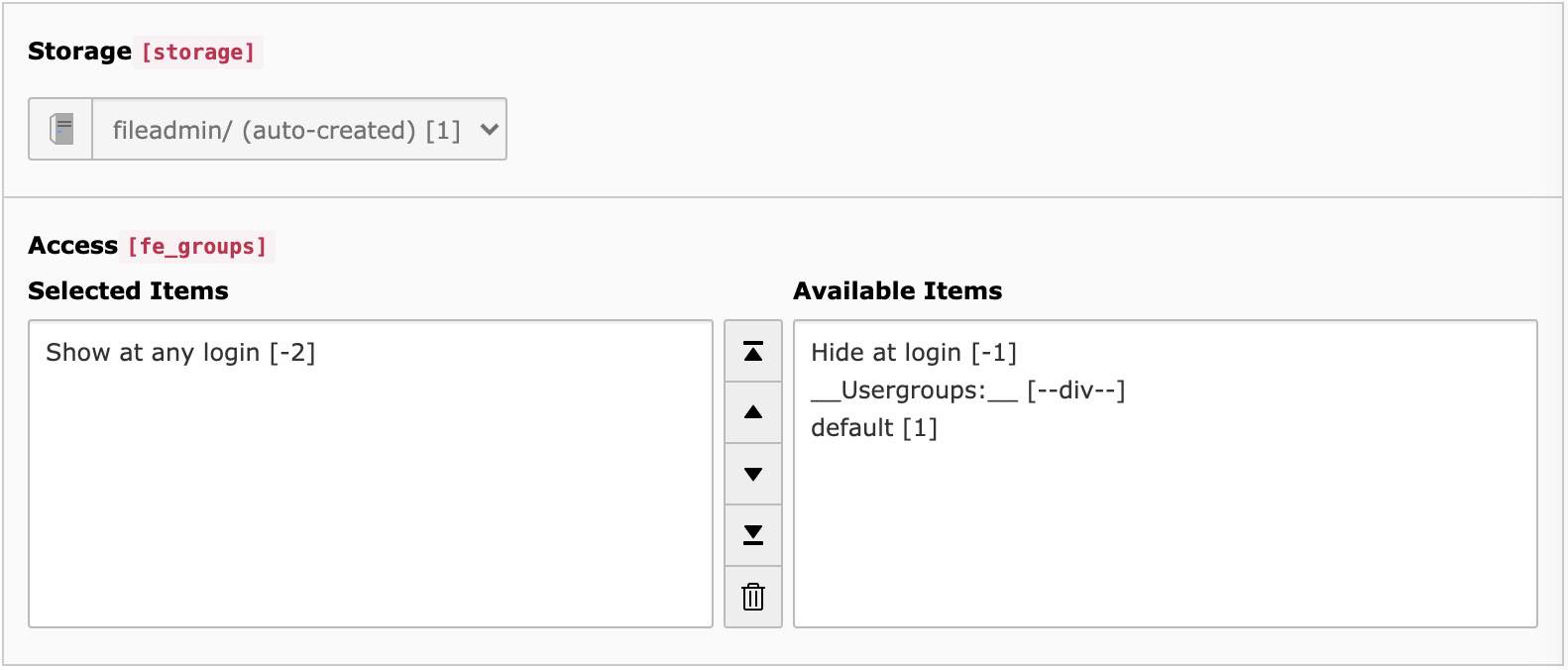
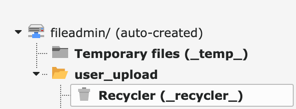
Protect everything within
/fileadmin/or other relative storages based on associated folder and file restrictions (visibility, user groups and dates of publication). - Keywords
-
FAL, files, directories, secure, security, protection
- Copyright
-
2020-2026
- Author
-
Xavier Perseguers
- License
-
This document is published under the Creative Commons BY 4.0 license.
- Rendered
-
Wed, 08 Apr 2026 12:34:46 +0000
Protect everything within /fileadmin/ based on associated folder and file restrictions (visibility, user groups and dates of publication).
Table of Contents: