Passkeys Backend Authentication
- Extension key
-
nr_passkeys_be
- Package name
-
netresearch/nr-passkeys-be
- Version
-
0.4
- Language
-
en
- Author
-
Netresearch DTT GmbH
- License
-
This document is published under the GPL-2.0-or-later license.
- Rendered
-
Tue, 17 Feb 2026 23:13:01 +0000
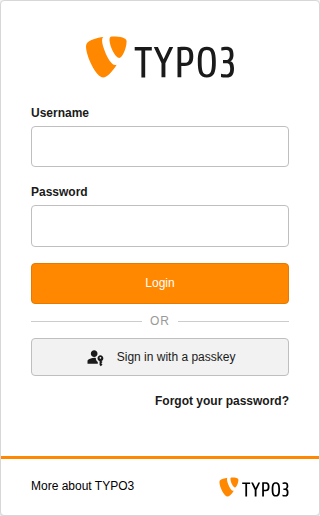
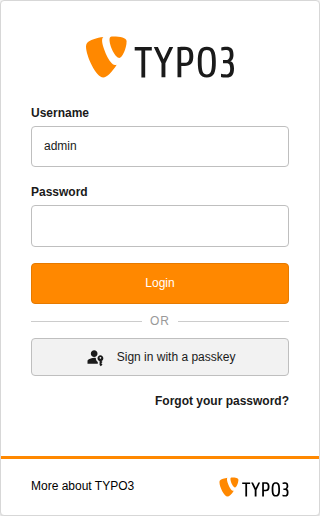
Passwordless TYPO3 backend authentication via WebAuthn/FIDO2 Passkeys. Enables one-click login with TouchID, FaceID, YubiKey, and Windows Hello -- directly on the standard TYPO3 login form.

The passkey button appears below the Login button with an "or" divider.
Introduction
Learn what the extension does, which authenticators and browsers are supported, and see the full feature list.
Installation
Install via Composer, activate the extension, and run the database schema update.
Configuration
Configure relying party, challenge TTL, discoverable login, rate limiting, account lockout, and cryptographic algorithms.
Usage
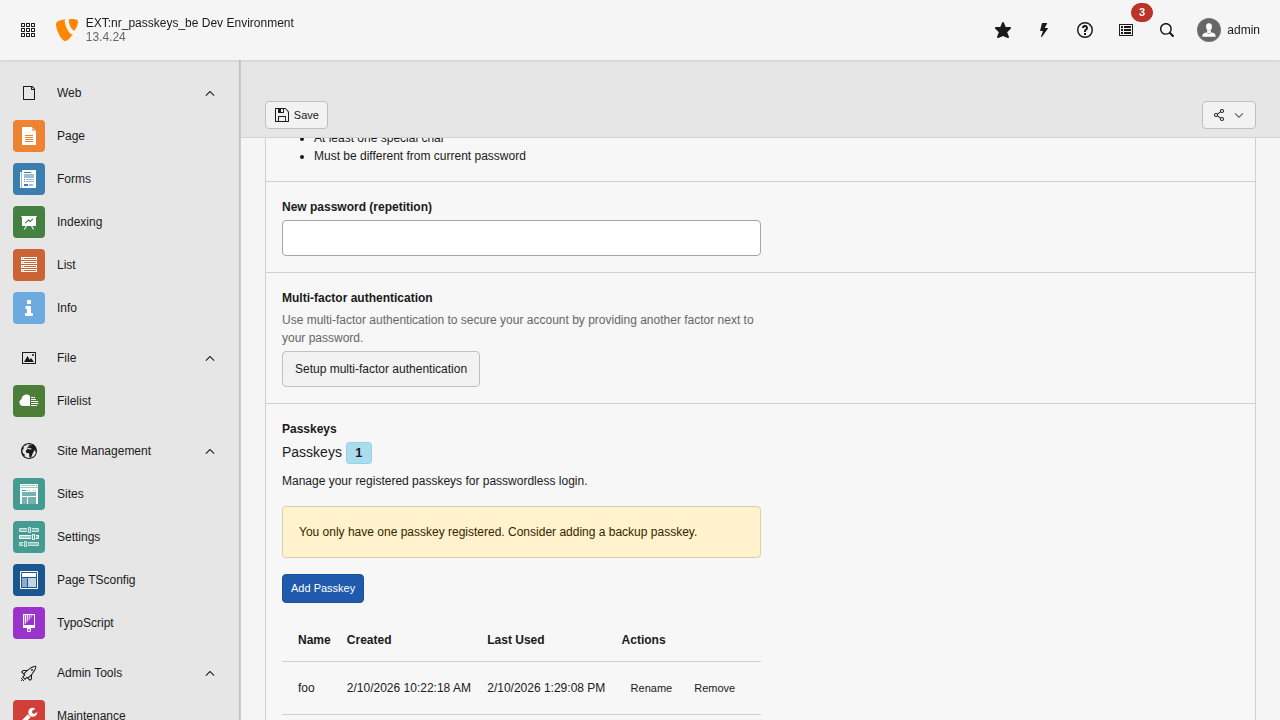
Register passkeys, log in with a single touch, and manage your credentials in User Settings.
Administration
Admin API for listing, revoking credentials and unlocking locked-out accounts.
Developer Guide
Architecture overview, authentication service, controllers, services, and how to run tests.
Security
WebAuthn security model, HMAC-signed challenges, rate limiting, and user enumeration prevention.
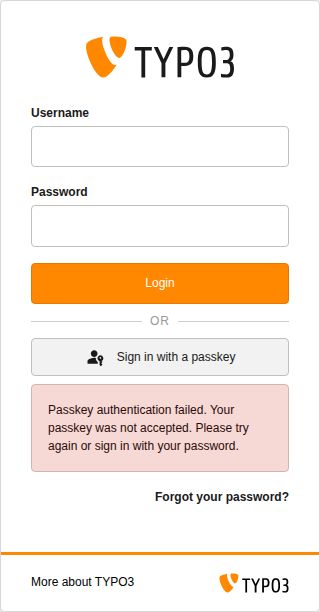
Troubleshooting
Common error messages, encryptionKey issues, HTTPS requirements, and debug logging.
Changelog
Version history and release notes.